AI-based pattern analysis traps attackers trying to abuse accounts
Barracuda Networks, Inc., a leading provider of cloud-first security solutions unveiled the findings of the first half of 2023 as AI-based pattern analysis helped Barracuda Managed XDR to detect and neutralize thousands of high-risk incidents in nearly one trillion IT events collected overall. The ability of artificial intelligence (AI) to build patterns of normal activity and identify anomalies makes it a powerful security tool when attackers try to abuse compromised accounts using legitimate credentials.
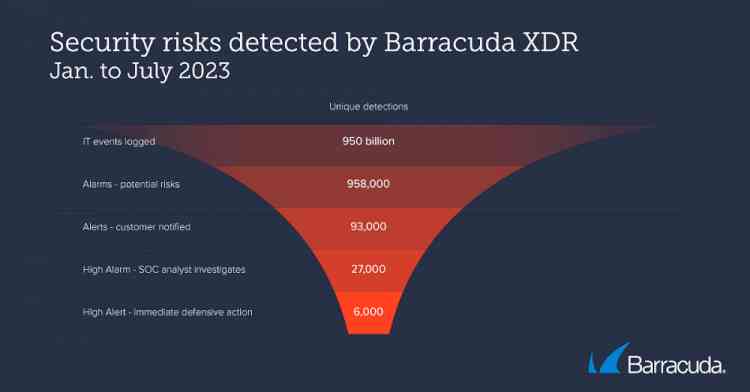
Barracuda Networks, Inc., a leading provider of cloud-first security solutions unveiled the findings of the first half of 2023 as AI-based pattern analysis helped Barracuda Managed XDR to detect and neutralize thousands of high-risk incidents in nearly one trillion IT events collected overall. The ability of artificial intelligence (AI) to build patterns of normal activity and identify anomalies makes it a powerful security tool when attackers try to abuse compromised accounts using legitimate credentials.
The three most common high-risk detections were “Impossible travel” login detection, “Anomaly” detection and Communication with known artifacts– defined as threats that required immediate defensive actions during the first six months of 2023
“Impossible travel” login detections occur when a user is trying to log into a cloud account from two geographically different locations in rapid succession – with the distance between them impossible to cover in the time between logins. While this can mean they are using a VPN for one of the sessions, it is often a sign that an attacker has gained access to a user's account.
“In one incident investigated by the SOC team, a user logged into their Microsoft 365 account from California, and then just thirteen minutes later from Virginia,” said Merium Khalid, Director, SOC Offensive Security, Barracuda. “To physically achieve this, they would have to travel at a speed exceeding 10,000 miles per hour. The IP used to log in from Virginia was not associated with a known VPN address and the user did not normally log in from this location. We notified the customer who confirmed that this was an unauthorized login and immediately reset their passwords and logged the rogue user out of all active accounts.”
“Anomaly” detections identify unusual or unexpected activity in a user's account. This could include things like rare or one-off login times, unusual file access patterns, or excessive account creation for an individual user or organization. Such detections can be a sign of a variety of problems, including malware infections, phishing attacks, and insider threats.
Communication with known malicious artifacts identify communication with red flagged or known malicious IP addresses, domains, or files. This can be a sign of a malware infection, or a phishing attack and you should immediately quarantine the computer.
“Everyone has a distinctive digital profile in terms of how, where and when they work. If an IT event falls outside these pattern perimeters the AI-based detection triggers an alert,” said Merium Khalid. “However, while AI can significantly enhance security, it can also be used for malicious purposes – to create highly convincing emails or adapt malicious code to specific targets or changing security conditions, for example. To secure your organization and employees against rapidly evolving, increasingly intelligent attack tactics, you need deep, multi-layered security that includes robust authentication measures, regular employee training and software updates, underpinned by full visibility and continuous monitoring across the network, applications, and endpoints.”



 City Air News
City Air News 










